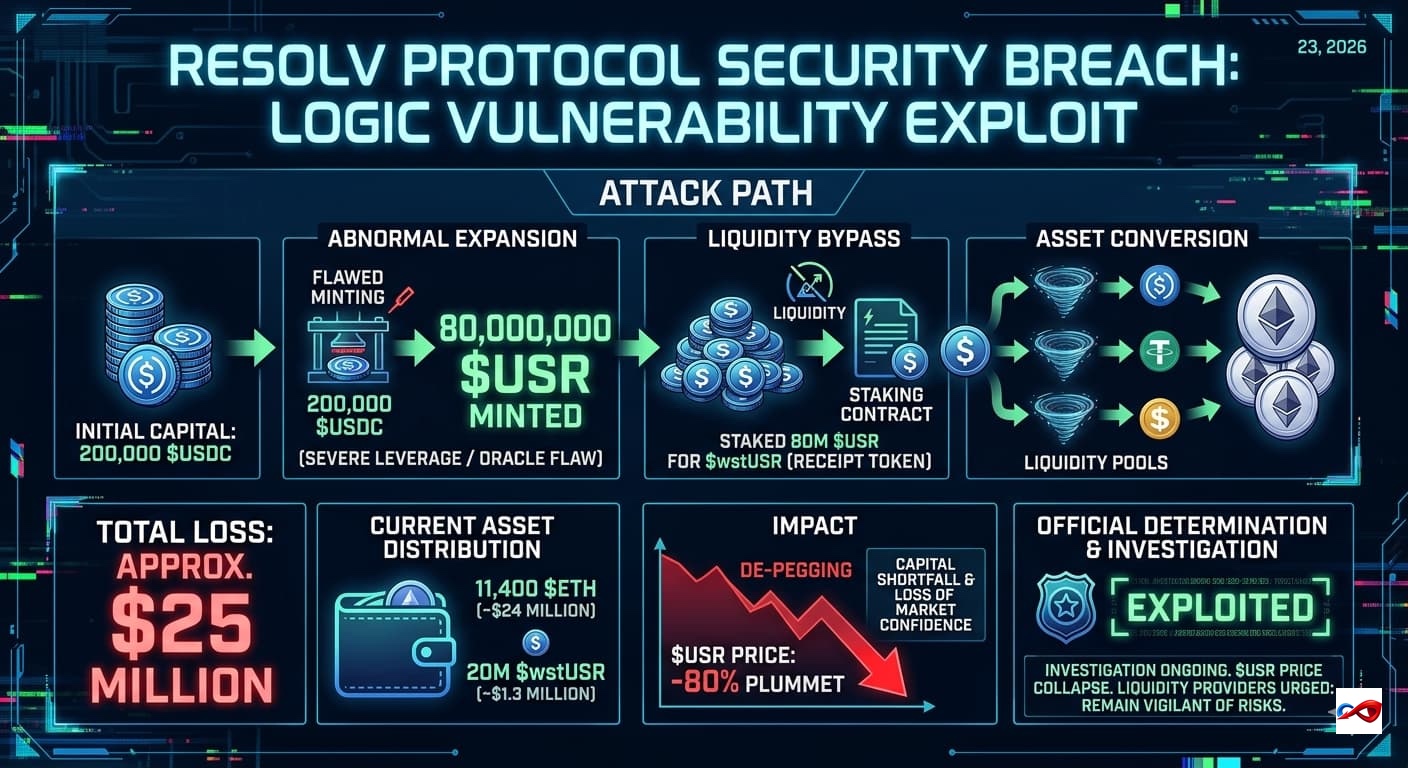
ResolvLabs Exploited: Total Losses Reach $25 Million
According to monitoring by PeckShieldAlert, ResolvLabs recently fell victim to a severe exploit. The attacker utilized 200,000 $USDC to manipulate the protocol's mechanisms, illicitly minting 80 million $USR.
SECURITY EVENTS