Keom Protocol Suffers Full-Drain
Redemption Attack, Resulting in $94k Loss
Based on Defimon Alerts monitoring,lending platform deployed on Polygon zkEVM, recently fell victim to an exploit. The incident resulted in a loss of approximately $94,000 due to a critical logic error within the contract’s asset redemption process.
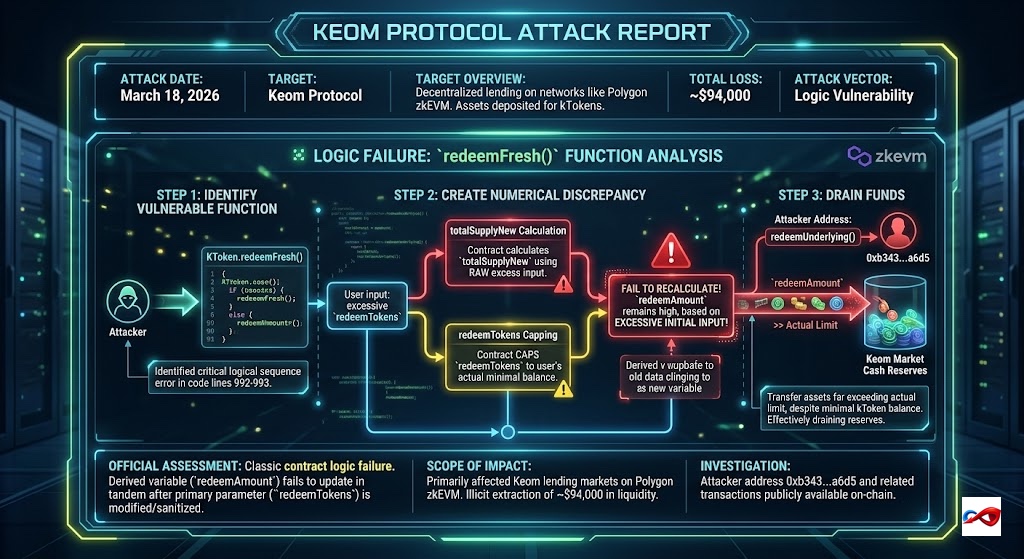
- Attack Date: March 18, 2026
- Target: Keom Protocol
- Target Overview: Keom Protocol is a decentralized lending protocol deployed on networks such as Polygon zkEVM. Users can deposit assets to receive kTokens and earn interest or use them as collateral for borrowing.
- Total Loss: ~$94,000
- Attack Vector: Logic Vulnerability
Incident Review and Technical Details
1. Attack Path:
- Identifying the Vulnerable Function: The attacker identified a critical logical sequence error within the
KToken.redeemFresh()function (Source code lines 992-993). - Creating Numerical Discrepancy: During the redemption process, the contract first calculates the new total supply (
totalSupplyNew) using the rawredeemTokensvalue provided by the user. However, while the contract subsequently caps theredeemTokensto the user's actual balance, it fails to synchronously recalculate the corresponding redemption amount (redeemAmount). - Draining Funds: Because the
redeemAmountremained at a high value based on the "excessive initial input," the attacker was able to trigger asset transfers far exceeding their actual limit by callingredeemUnderlying(), despite holding a minimal kToken balance. This effectively drained the market's cash reserves.
2. Scope of Impact: The attack primarily affected Keom lending markets on Polygon zkEVM, resulting in the illicit extraction of approximately $94,000 in liquidity from the protocol.
3. Official Assessment: The vulnerability is classified as a classic contract logic failure, specifically where a derived variable fails to update in tandem after the primary parameter it depends on has been modified/sanitized.
4. Investigation Progress: The attacker’s address (0xb343...a6d5) and related transactions are publicly available on-chain.
AUTOSEC.DEV Solution: Building a 360-Degree Defense
To counter hybrid attacks involving "Web2 Breach + Web3 Monetization," AUTOSEC.DEV provides comprehensive protection from code to personnel:
- Team OPSEC (Operations Security) Audit & Hardening: We provide enterprise-grade security training and configuration for core Web3 team members. We assist teams in deploying security hardware and risk detection software to increase the difficulty of social engineering attacks, while auditing password management protocols and device security policies.
- End-to-End Incident Response (IR): In an emergency, every second of confusion amplifies the loss. AUTOSEC.DEV provides standardized SOPs (Standard Operating Procedures) and rapid response services tailored to specific business needs to help projects mitigate losses quickly.
Service Content
- AUTOSEC.DEV - Security Awareness Training
- AUTOSEC.DEV - Incident Response Service
- AUTOSEC.DEV - Security Strategy & Planning