• 3 min read
dTRINITY Suffers
~$260k Loss in Logic Vulnerability
The dLEND module, under the DeFi protocol dTRINITY, has incurred approximately $257,000 in bad debt** due to a Logic Vulnerability The attacker executed a precise exploit against the cbBTC liquidity pool, which had been deployed for only six days and suffered from severe liquidity fragmentation.
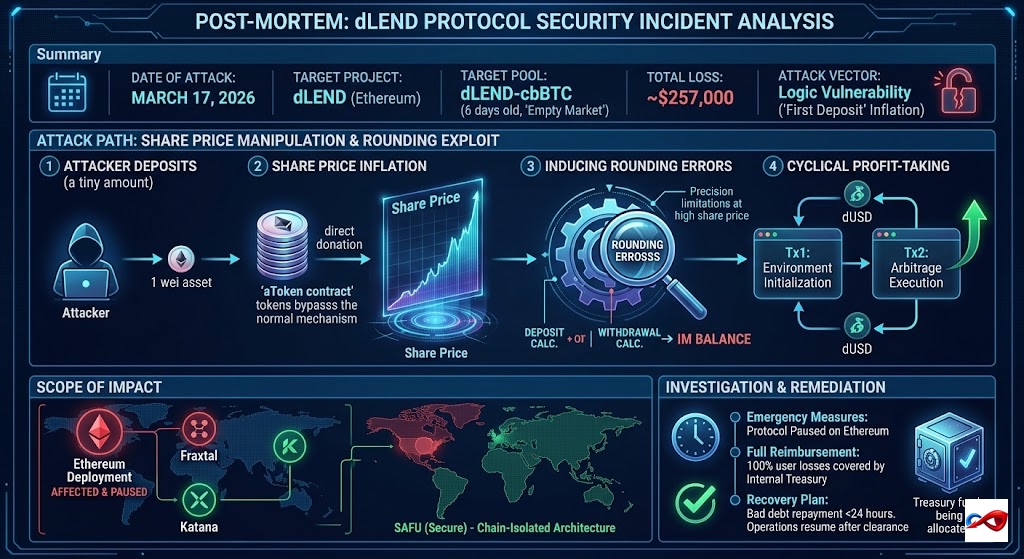
- Date of Attack: March 17, 2026
- Target Project: dLEND
- Target Overview: dLEND is a lending protocol based on an Aave fork. The affected dLEND-cbBTC pool had been deployed for only 6 days. Due to extremely low initial liquidity, it was in a classic "Empty Market" state.
- Total Loss: ~$257,000
- Attack Vector: Logic Vulnerability
Incident Review & Technical Details
-
Attack Path:
- Low Liquidity Entry: The attacker targeted the
dLEND-cbBTCpool, which lacked sufficient liquidity due to its recent launch. - Share Price Manipulation: The attacker first deposited a negligible amount (e.g., 1 wei) of assets, then "donated" a large volume of tokens directly to the
aTokencontract via atransfer. This non-standard donation inflated the Share Price of theaTokento astronomical levels. - Inducing Rounding Errors: Against the backdrop of an extremely high share price, the protocol’s accounting scaling logic for deposits and withdrawals triggered rounding imbalances due to precision limitations.
- Cyclical Profit-Taking: The attacker exploited this imbalance to ensure that each "Deposit-Withdraw" cycle extracted slightly more assets than the cost. Through two key transactions (Tx1 for environment initialization and Tx2 for arbitrage execution), the available dUSD liquidity in the pool was repeatedly drained.
- Low Liquidity Entry: The attacker targeted the
-
Scope of Impact:
- Affected Area: Limited to the dLEND deployment on Ethereum.
- Secure Area: Deployments on Fraxtal and Katana remain SAFU (Secure) due to the chain-isolated architecture.
-
Official Verdict:
- Confirmed as an exploitation of the "First Deposit" inflation vulnerability, a known risk factor in certain Aave-forked protocols.
-
Investigation & Remediation:
- Emergency Measures: Protocol operations on Ethereum have been paused.
- Full Reimbursement: The official team has declared that Internal Treasury funds will be used to cover 100% of user losses.
- Recovery Plan: Bad debt repayment will commence within 24 hours. Protocol operations will resume once the debt is cleared.
AUTOSEC.DEV Solution: Building a 360-Degree Defense
To counter hybrid attacks involving "Web2 Breach + Web3 Monetization," AUTOSEC.DEV provides comprehensive protection from code to personnel:
- Team OPSEC (Operations Security) Audit & Hardening: We provide enterprise-grade security training and configuration for core Web3 team members. We assist teams in deploying security hardware and risk detection software to increase the difficulty of social engineering attacks, while auditing password management protocols and device security policies.
- End-to-End Incident Response (IR): In an emergency, every second of confusion amplifies the loss. AUTOSEC.DEV provides standardized SOPs (Standard Operating Procedures) and rapid response services tailored to specific business needs to help projects mitigate losses quickly.
Service Content
- AUTOSEC.DEV - Security Awareness Training
- AUTOSEC.DEV - Incident Response Service
- AUTOSEC.DEV - Security Strategy & Planning