Security Alert: North Korean Threat Actor
FAMOUS CHOLLIMA Releases 26 Malicious npm Packages
Security researchers have detected a large-scale supply chain attack on the official npm registry orchestrated by the North Korean-linked threat group **FAMOUS CHOLLIMA** (also known as LabP2P). The group released at least **26 malicious packages** masquerading as legitimate development tools. These packages utilize `install.js` scripts to automatically trigger Remote Access Trojans (RATs) upon installation, aiming to exfiltrate developers' SSH keys, Git repositories, browser credentials, and sensitive clipboard data.
- Release Date: March 3, 2026
- Risk Level: Critical
- CVE ID: N/A
- Vulnerability Category: Supply Chain Attack
Affected Scope
Vulnerability Details
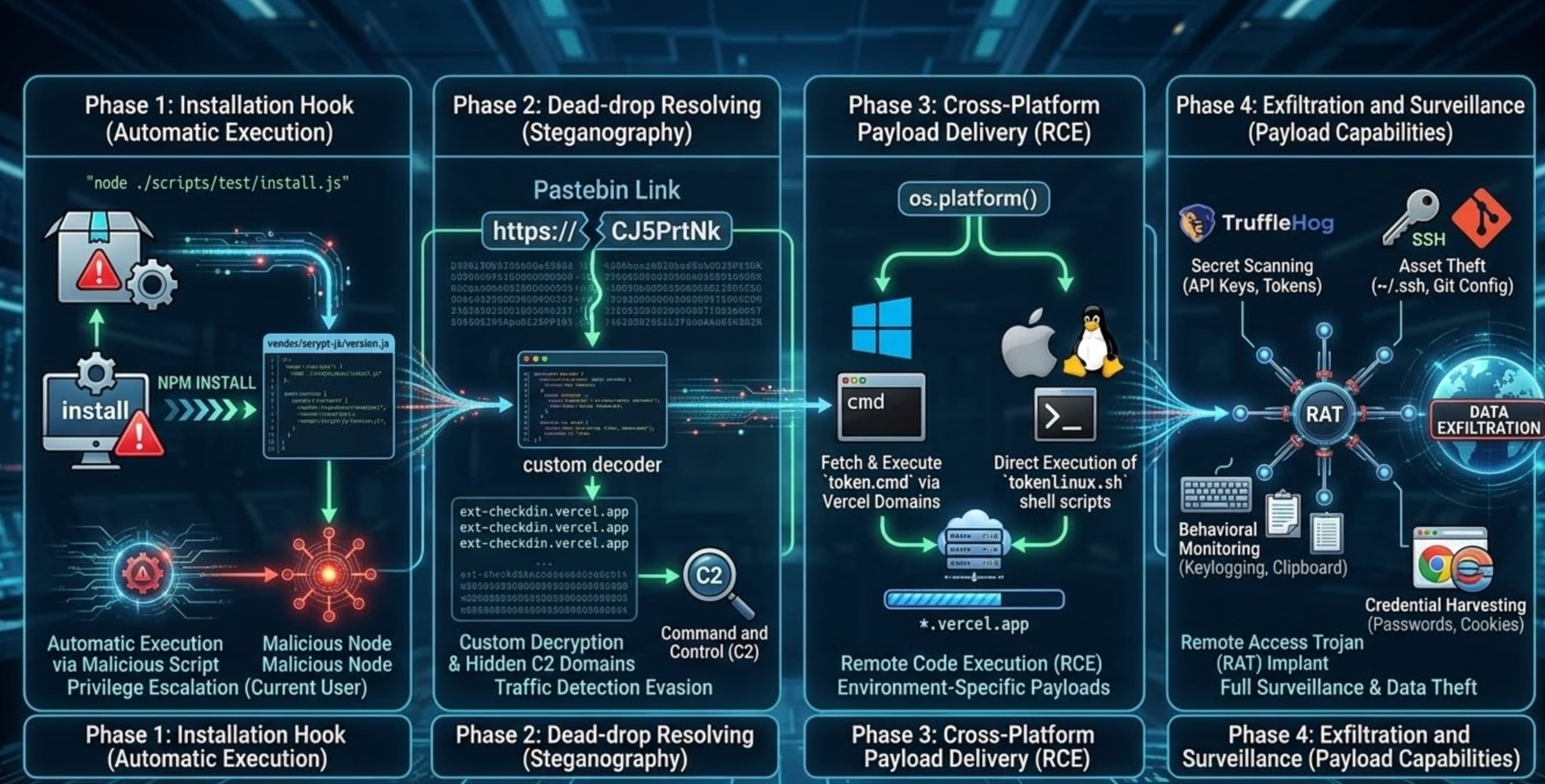
Phase 1: Installation Hook (Automatic Execution)
All affected packages contain a malicious install script: "node ./scripts/test/install.js". By default, npm executes this script with the current user's privileges during the installation process, which subsequently invokes core malicious code hidden within vendor/scrypt-js/version.js.
Phase 2: Dead-drop Resolving (Steganography)
The malicious code downloads seemingly legitimate text from Pastebin links (e.g., CJ5PrtNk) and uses a custom decoder to extract hidden Command and Control (C2) domains. This steganographic technique is highly effective at evading static traffic detection.
Payload Download Addresses:
ext-checkdin.vercel.app
cleverstack-ext301.vercel.app
cleverstack-app998.vercel.app
brightlaunch-ext742.vercel.app
brightlaunch-app615.vercel.app
primevector-ext483.vercel.app
primevector-app920.vercel.app
zenithflow-ext156.vercel.app
zenithflow-app877.vercel.app
cloudharbor-ext664.vercel.app
cloudharbor-app239.vercel.app
sparkforge-ext518.vercel.app
sparkforge-app790.vercel.app
logicfield-ext432.vercel.app
logicfield-app681.vercel.app
atlasnode-ext957.vercel.app
atlasnode-app204.vercel.app
signalbase-ext369.vercel.app
signalbase-app845.vercel.app
neuraldock-ext126.vercel.app
neuraldock-app734.vercel.app
orbitstack-ext592.vercel.app
orbitstack-app318.vercel.app
fusionlayer-ext807.vercel.app
fusionlayer-app463.vercel.app
quantapath-ext275.vercel.app
quantapath-app914.vercel.app
visiondock-ext648.vercel.app
visiondock-app157.vercel.app
openmatrix-ext539.vercel.app
openmatrix-app882.vercel.app
Phase 3: Cross-Platform Payload Delivery (RCE)
After identifying the environment via os.platform(), the script uses curl or wget to fetch targeted payloads from *.vercel.app domains:
- Windows: Executes a
cmdscript to silently download and runtoken.cmd. - macOS/Linux: Uses a
bashpipe to directly execute remote shell scripts (e.g.,tokenlinux.sh).
Phase 4: Exfiltration and Surveillance (Payload Capabilities) The final Remote Access Trojan (RAT) implant possesses the following malicious capabilities:
- Secret Scanning: Integrates TruffleHog to scan code for sensitive secrets (API Keys, Tokens).
- Asset Theft: Extracts SSH keys (
~/.ssh) and Git configuration files. - Behavioral Monitoring: Performs keylogging and captures real-time clipboard contents.
- Credential Harvesting: Exports saved usernames, passwords, and cookies from web browsers.
Remediation Recommendations
- Complete Uninstallation: Run
npm uninstall <malicious_package_name>and manually delete the entirenode_modulesdirectory to ensure no artifacts remain. - Persistence Cleanup:
- Unix/macOS: Check for and delete
$HOME/.config/tokenlinux.shor$HOME/Library/tokenlinux.sh. - Windows: Check for and delete
%APPDATA%\token.cmd.
- Unix/macOS: Check for and delete
- Credential Rotation: Given the keylogging and credential-stealing capabilities of this RAT, affected users must immediately rotate Git Access Tokens, SSH Private Keys, Cloud Service API Keys, and any sensitive passwords stored in browsers.
AUTOSEC.DEV Solution: Building a 360-Degree Defense
- Secure Code Review: To defend against NPM supply chain poisoning, we combine automated static analysis with expert manual review to thoroughly assess your application's source code and third-party dependencies. We identify malicious packages, hidden backdoors, and logic errors introduced by attackers, eliminating security risks at the development stage before they compromise developer environments or production systems.
- Security Awareness Training & Phishing Simulation : FAMOUS CHOLLIMA heavily relies on social engineering—such as fake job interviews or fraudulent coding tasks—to trick developers into downloading poisoned NPM packages. We design realistic phishing campaigns and deliver role-based security training to measure and improve developer susceptibility, establishing a strong "human firewall" against targeted social engineering attacks.
- End-to-End Incident Response (IR): In an emergency, every second of confusion amplifies the loss. AUTOSEC.DEV provides standardized SOPs (Standard Operating Procedures) and rapid response services tailored to specific business needs to help projects mitigate losses quickly.
AUTOSEC.DEV Solution: Building a 360-Degree Defense
- Secure Code Review: To defend against NPM supply chain poisoning, we combine automated static analysis with expert manual review to thoroughly assess your application's source code and third-party dependencies. We identify malicious packages, hidden backdoors, and logic errors introduced by attackers, eliminating security risks at the development stage before they compromise developer environments or production systems.
- Security Awareness Training & Phishing Simulation : FAMOUS CHOLLIMA heavily relies on social engineering—such as fake job interviews or fraudulent coding tasks—to trick developers into downloading poisoned NPM packages. We design realistic phishing campaigns and deliver role-based security training to measure and improve developer susceptibility, establishing a strong "human firewall" against targeted social engineering attacks.
- End-to-End Incident Response (IR): In an emergency, every second of confusion amplifies the loss. AUTOSEC.DEV provides standardized SOPs (Standard Operating Procedures) and rapid response services tailored to specific business needs to help projects mitigate losses quickly.