• 3 min read
HB Token Suffers Flash
Loan State Manipulation Attack
According to monitoring by ExVul, the HB Token protocol on BNB Chain has fallen victim to a textbook Flash Loan State Manipulation attack, resulting in a cumulative loss of approximately 194,000 USDT.
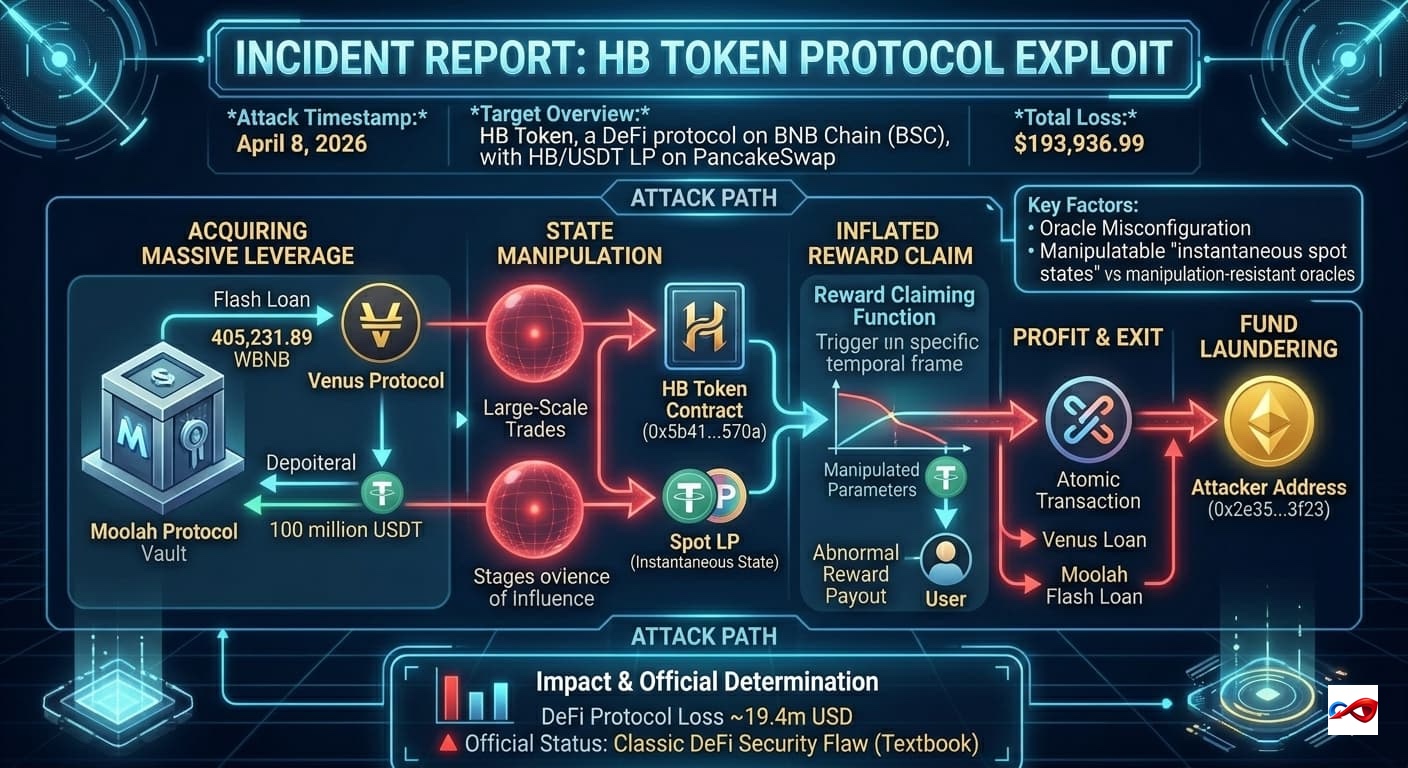
- Attack Timestamp: April 8, 2026
- Target: HB Token
- Target Overview: HB Token is a DeFi protocol deployed on the BNB Chain (BSC), encompassing the HB token, a reward distribution system, and HB/USDT liquidity pools on decentralized exchanges (DEXs) such as PancakeSwap.
- Loss Amount: $193,936.99
- Attack Vector: Oracle Misconfiguration
Incident Review & Technical Details
- Attack Path:
- Acquiring Massive Leverage: The attacker first initiated a flash loan of 405,231.89 WBNB from the Moolah protocol, subsequently depositing it into the Venus protocol as collateral to borrow 100 million USDT, securing significant capital depth for pool manipulation.
- State Manipulation: The attacker interacted with the HB Token-related contract (0x5b41...570a) and the reward proxy contract using these massive funds. Because the project’s reward accounting system erroneously relied on the instantaneous state of the Spot Liquidity Pool (Spot LP), the attacker was able to distort reward calculation parameters via large-scale trades.
- Inflated Reward Claim: At the exact "frame" where the calculation logic was manipulated, the attacker triggered the reward claiming function. This caused the system to falsely verify the attacker's entitlement to massive rewards, resulting in the extraction of an abnormal volume of assets from the protocol.
- Profit & Exit: The attacker withdrew USDT from the HB/USDT LP and, within a single transaction (atomic transaction), repaid the Venus loan and the Moolah flash loan.
- Fund Laundering: The final profit of 193,936.99 USDT was transferred to the attacker-controlled address (0x2e35...3f23).
- Impact: The exploit resulted in a loss of approximately $194,000 for the HB Token protocol, causing a severe financial impact on the HB token and its liquidity pools.
- Official Determination: This vulnerability is a textbook DeFi security flaw, specifically the use of manipulatable "instantaneous spot states" in critical reward/pricing accounting logic instead of manipulation-resistant oracles.
- Investigation Progress: The protocol remains at extreme security risk unless the project team refactors its reward algorithm to remove the dependency on spot LP states.
AUTOSEC.DEV Solution: Building a 360-Degree Defense
To counter hybrid attacks involving "Web2 Breach + Web3 Monetization," AUTOSEC.DEV provides comprehensive protection from code to personnel:
- Team OPSEC (Operations Security) Audit & Hardening: We provide enterprise-grade security training and configuration for core Web3 team members. We assist teams in deploying security hardware and risk detection software to increase the difficulty of social engineering attacks, while auditing password management protocols and device security policies.
- End-to-End Incident Response (IR): In an emergency, every second of confusion amplifies the loss. AUTOSEC.DEV provides standardized SOPs (Standard Operating Procedures) and rapid response services tailored to specific business needs to help projects mitigate losses quickly.
Service Content
- AUTOSEC.DEV - Security Awareness Training
- AUTOSEC.DEV - Incident Response Service
- AUTOSEC.DEV - Security Strategy & Planning