The DBXen protocol was hit by an ERC-2771 identity
obfuscation attack, resulting in a loss of approximately $150,000.
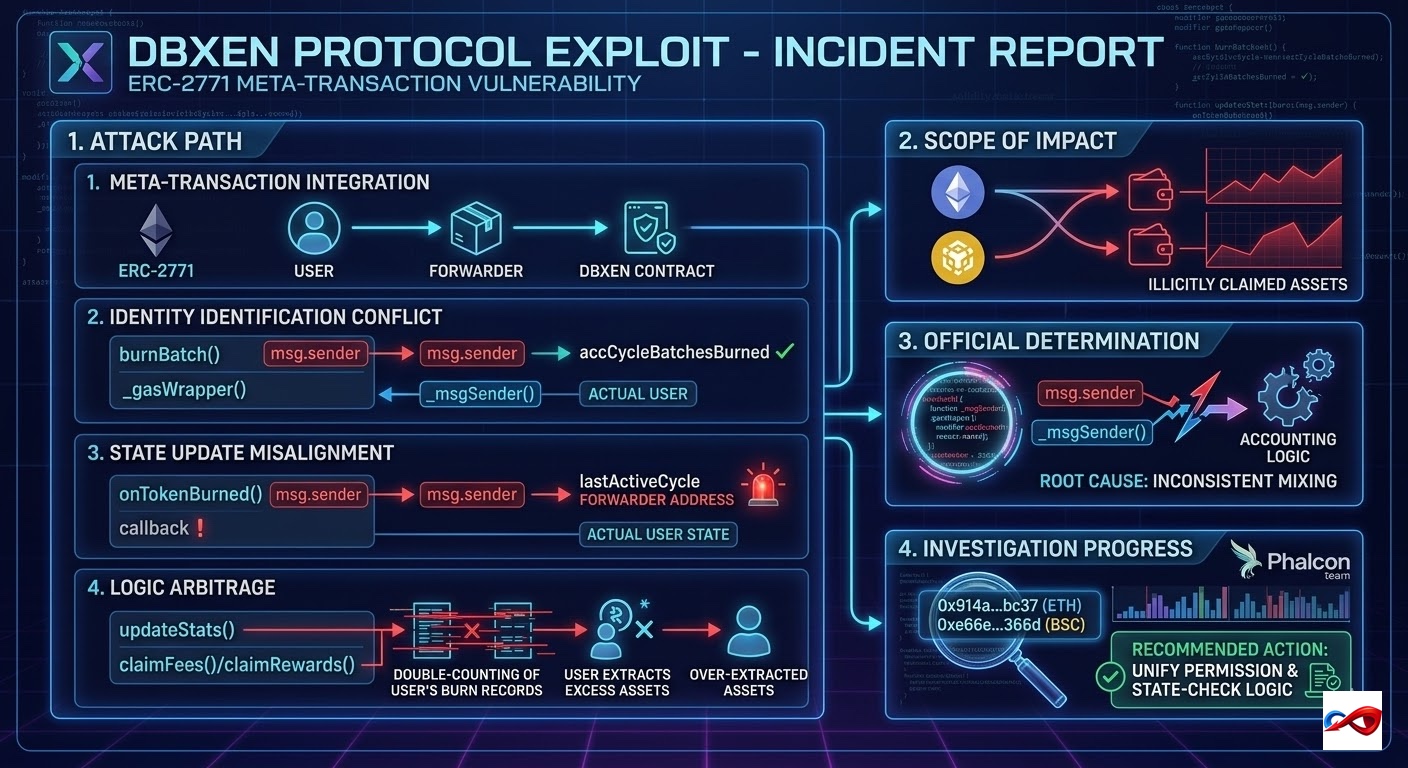
According to monitoring by BlockSec Phalcon, the DBXen protocol suffered from an identity verification inconsistency due to the mixed use of _msgSender() and msg.sender during meta-transaction processing. The attacker exploited this logic vulnerability to manipulate reward settlements, illicitly extracting approximately $150,000 in assets from contracts on both the Ethereum and BSC chains.
- Exploit Date: March 12, 2026
- Target: DBXen
- Target Overview: DBXen is a multi-chain decentralized yield generation protocol that allows users to participate in periodic reward distributions by burning tokens.
- Total Loss: ~$150,000
- Attack Vector: Logic Vulnerability
Incident Review and Technical Details
1. Attack Path
- Meta-Transaction Integration: The DBXen protocol integrated the ERC-2771 standard to support gasless transactions. In its processing logic, the contract must distinguish between the Forwarder address (
msg.sender) and the Actual user address (_msgSender()). - Identity Identification Conflict: During the execution of the
burnBatch()function, thegasWrapper()modifier correctly utilized_msgSender()to identify the actual user and incremented theiraccCycleBatchesBurned(accumulated cycle batches burned). - State Update Misalignment: However, the subsequent burn callback,
onTokenBurned(), erroneously used the nativemsg.sender. Since the request was sent via a forwarder, the system updated thelastActiveCycle(last active cycle) for the Forwarder address, while the actual user’s state bit remained unchanged (retaining its old value). - Logic Arbitrage: When calling
claimFees()orclaimRewards(), theupdateStats()function encountered a logic error. Because the user’s burn records had increased but their active cycle was not marked as processed, the system allowed the attacker to double-count and over-extract reward assets.
2. Scope of Impact
The exploit primarily affected contracts on Ethereum and BNB Smart Chain (BSC), leading to the illicit claiming of assets within the reward pools.
3. Official Determination
The root cause was the inconsistent mixing of _msgSender() and msg.sender within the same transaction flow, causing the Accounting Logic to fail under a meta-transaction environment.
AUTOSEC.DEV Solution: Building a 360-Degree Defense
To counter hybrid attacks involving "Web2 Breach + Web3 Monetization," AUTOSEC.DEV provides comprehensive protection from code to personnel:
- Team OPSEC (Operations Security) Audit & Hardening: We provide enterprise-grade security training and configuration for core Web3 team members. We assist teams in deploying security hardware and risk detection software to increase the difficulty of social engineering attacks, while auditing password management protocols and device security policies.
- End-to-End Incident Response (IR): In an emergency, every second of confusion amplifies the loss. AUTOSEC.DEV provides standardized SOPs (Standard Operating Procedures) and rapid response services tailored to specific business needs to help projects mitigate losses quickly.
Service Content
- AUTOSEC.DEV - Security Awareness Training
- AUTOSEC.DEV - Incident Response Service
- AUTOSEC.DEV - Security Strategy & Planning