• 3 min read
SquidMulticall
Vulnerability Leads to Million-Dollar Exploit
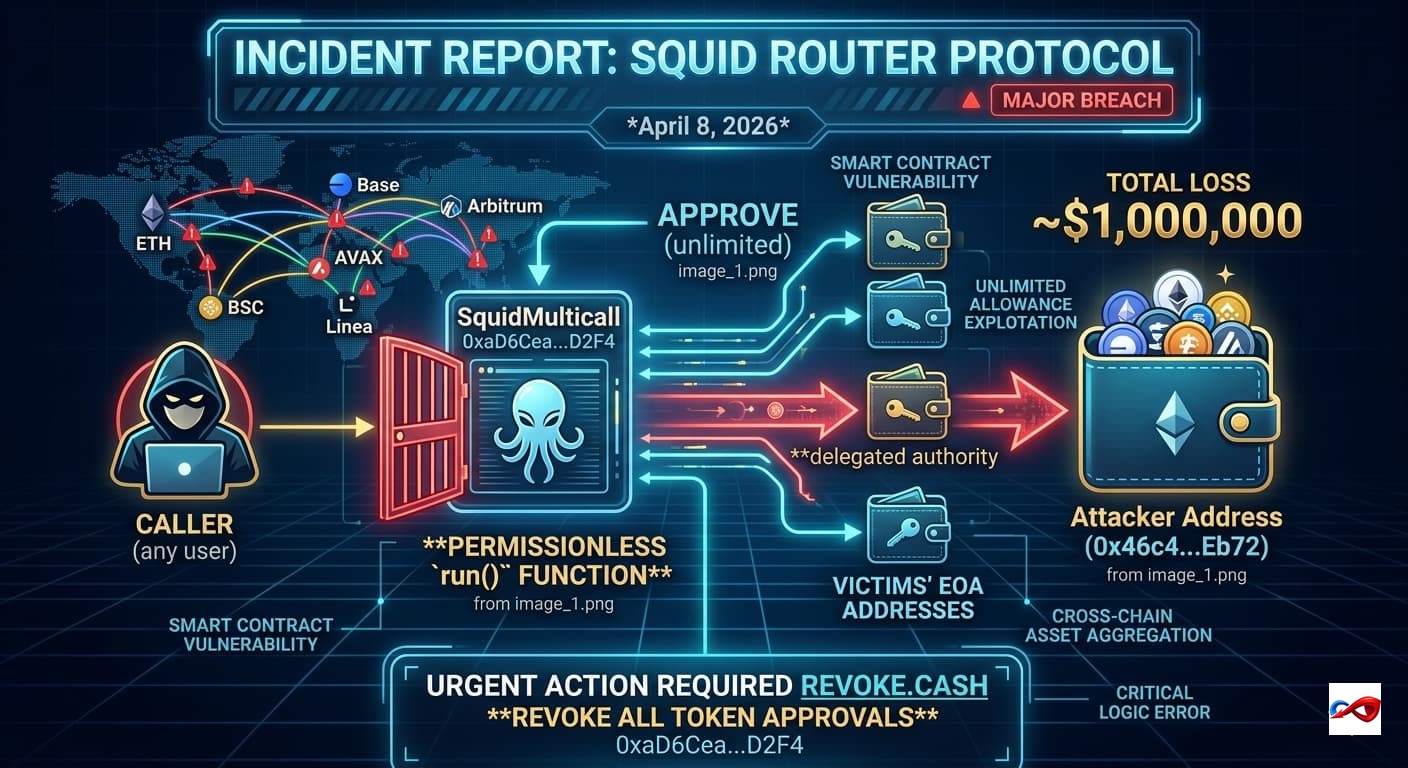
According to monitoring by ExVul, the cross-chain protocol Squid Router has suffered a major security breach. Hackers are exploiting a logic flaw in the SquidMulticall contract to remotely drain assets from wallets that have previously granted approvals to the protocol.
- Attack Date: April 8, 2026
- Target: Squid Router
- Target Overview: Squid Router is a cross-chain interoperability protocol. Its
SquidMulticallcontract (0xaD6Cea...D2F4) is designed to facilitate multi-chain, multi-step contract interactions through a single entry point. - Total Loss: ~$1,000,000
- Attack Vector: Smart Contract Vulnerability
Incident Review & Technical Details
- Attack Path:
- Identification of Vulnerable Function: The attacker identified that the
SquidMulticall.run()function was entirely permissionless. While the function was designed to execute arbitrary external calls, it lacked any validation of the caller (msg.sender). - Crafting Malicious Calldata: The attacker targeted victim addresses that had previously granted "unlimited allowance" to the contract. They crafted specific calldata that instructed the contract to invoke the
transferFromfunction on various token contracts (e.g., USDC, USDT). - Exploitation of Allowance: Since victims had granted unlimited approvals to
SquidMulticallduring previous interactions with Squid Router, the contract used its delegated authority to move the victims' funds to the attacker’s address whenrun()was executed. - Cross-Chain Asset Aggregation: Exploiting the identical contract addresses and logic across multiple chains (ETH, AVAX, BSC, Base, Linea, and Arbitrum), the attacker launched synchronized exploit transactions.
- Liquidation: Assets were transferred directly to attacker-controlled wallets (e.g.,
0x46c4...Eb72). A single transaction was sufficient to drain a victim's entire balance across multiple chains.
- Identification of Vulnerable Function: The attacker identified that the
- Scope of Impact: Multiple EOA (Externally Owned Account) addresses were drained across various chains, resulting in a total loss of approximately $1 million.
- Official Assessment: The incident is classified as a critical logic error in the smart contract code. The core issue is that the contract allowed any arbitrary user to execute instructions as the contract entity via the
run()function, failing to restrict access to authorized routers or specific users. - Investigation Status: Project teams and security experts are urging all users who have ever interacted with Squid Router to immediately visit Revoke.cash to check and revoke all token approvals for the contract address
0xaD6Cea45f98444a922a2b4fE96b8C90F0862D2F4to prevent further losses.
AUTOSEC.DEV Solution: Building a 360-Degree Defense
To counter hybrid attacks involving "Web2 Breach + Web3 Monetization," AUTOSEC.DEV provides comprehensive protection from code to personnel:
- Team OPSEC (Operations Security) Audit & Hardening: We provide enterprise-grade security training and configuration for core Web3 team members. We assist teams in deploying security hardware and risk detection software to increase the difficulty of social engineering attacks, while auditing password management protocols and device security policies.
- End-to-End Incident Response (IR): In an emergency, every second of confusion amplifies the loss. AUTOSEC.DEV provides standardized SOPs (Standard Operating Procedures) and rapid response services tailored to specific business needs to help projects mitigate losses quickly.
Service Content
- AUTOSEC.DEV - Security Awareness Training
- AUTOSEC.DEV - Incident Response Service
- AUTOSEC.DEV - Security Strategy & Planning