• 3 min read
Social Engineering Trap: Kraken Whale Targeted in Deep
Orchestration; $18.2 Million Laundered via THORChain Cross-Chain Swaps
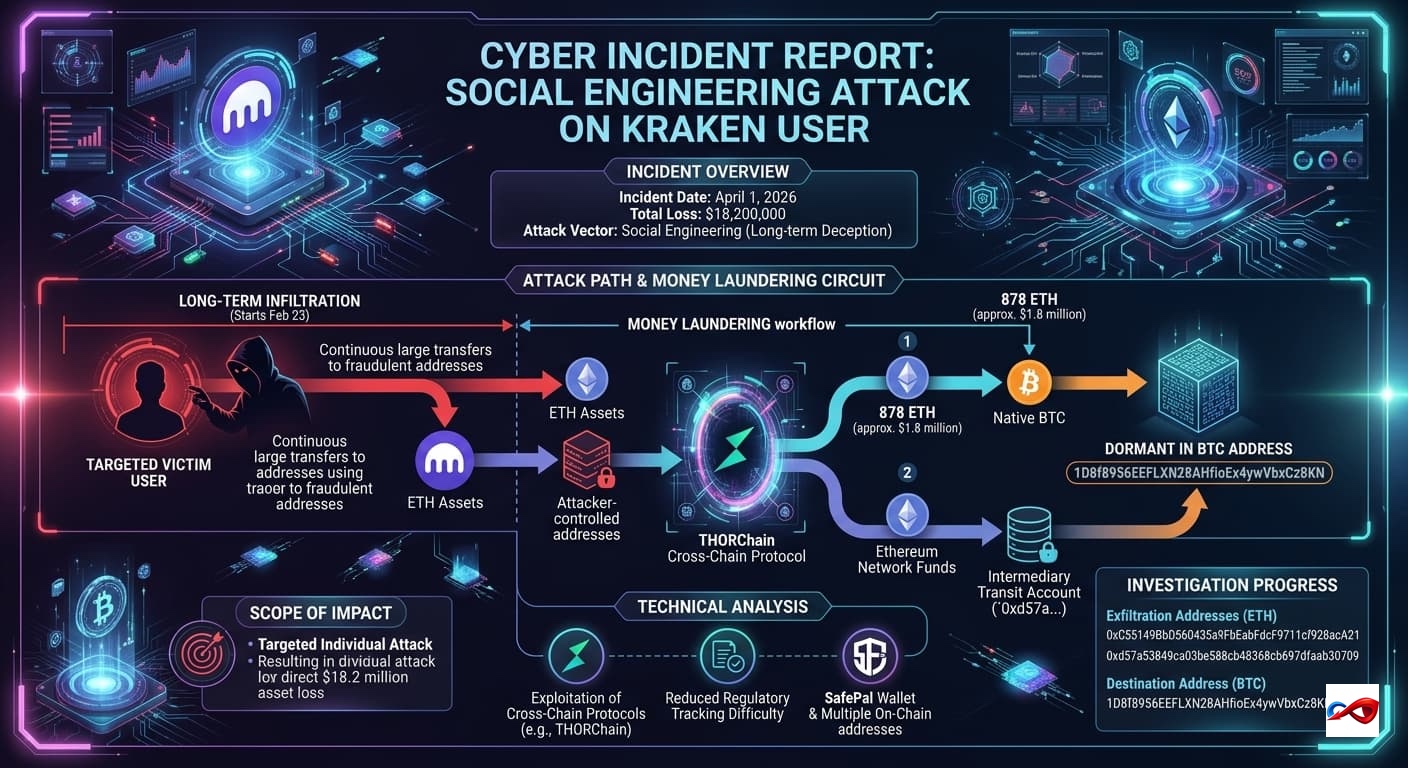
According to monitoring by Hacken,Since February 2026, a Kraken user fell victim to a sophisticated social engineering scheme orchestrated by attackers. Over several weeks, the individual cumulatively transferred approximately $18.2 million to fraudulent addresses across multiple transactions.
- Incident Date: April 1, 2026
- Target: Kraken Exchange User
- Target Overview: The victim is an individual user of the Kraken platform. Through long-term social engineering infiltration, the attacker manipulated the victim into making continuous large-scale transfers to fraudulent addresses over an extended timeframe.
- Total Loss: $18,200,000
- Attack Vector: Social Engineering
Incident Review & Technical Details
-
Attack Path:
- Long-term Infiltration: Based on on-chain data tracking, this was not a single-event exploit. The victim began transferring funds to attacker-controlled addresses as early as February 23, characterizing this as a classic, long-term social engineering scam predicated on trust or deception.
- Money Laundering Circuit: After securing the funds, the attacker employed a complex laundering path to evade tracking. The core workflow is:
ETH Assets→THORChain→Native BTC. - Cross-Chain Asset Movement:
- The attacker has converted 878 ETH (approx. $1.8 million) into Bitcoin via THORChain. These funds are currently dormant in the destination BTC address.
- The remaining funds on the Ethereum network have been consolidated and transferred to an intermediary transit account (
0xd57a...).
-
Scope of Impact: This was a targeted attack against an individual, resulting in a direct asset loss of approximately $18.2 million for the Kraken user.
-
Technical Analysis:
- Exploitation of Cross-Chain Protocols: The attacker utilized decentralized protocols like THORChain, leveraging features such as "instant execution" and "direct native asset conversion." This effectively reduced the friction of cross-ecosystem laundering and increased the difficulty of regulatory tracking and forensics.
- Tooling: The incident involved the SafePal wallet environment and multiple on-chain interaction addresses.
-
Investigation Progress:
- Exfiltration Addresses (ETH):
0xC55149BbD560435a9FbEabFdcF9711cf928acA210xd57a53849ca03be588cb48368cb697dfaab30709
- Destination Address (BTC):
1D8f8956EEFLXN28AHfioEx4ywVbxCz8KN
- Exfiltration Addresses (ETH):
AUTOSEC.DEV Solution: Building a 360-Degree Defense
To counter hybrid attacks involving "Web2 Breach + Web3 Monetization," AUTOSEC.DEV provides comprehensive protection from code to personnel:
- Team OPSEC (Operations Security) Audit & Hardening: We provide enterprise-grade security training and configuration for core Web3 team members. We assist teams in deploying security hardware and risk detection software to increase the difficulty of social engineering attacks, while auditing password management protocols and device security policies.
- End-to-End Incident Response (IR): In an emergency, every second of confusion amplifies the loss. AUTOSEC.DEV provides standardized SOPs (Standard Operating Procedures) and rapid response services tailored to specific business needs to help projects mitigate losses quickly.
Service Content
- AUTOSEC.DEV - Security Awareness Training
- AUTOSEC.DEV - Incident Response Service
- AUTOSEC.DEV - Security Strategy & Planning